Download our FREE report “How to Create An Effective Cybersecurity Plan” and register to get a FREE high-level assessment of your vulnerabilities.
Have you thought about how much your company’s data is worth on the dark web?
At Nieto, our cybersecurity experts are keeping a close eye on the environment. Ransomware attacks have been evolving pretty aggressively. Thus making your data a prime target for users of the dark web.
How are cyber-thieves operating?
- Double & Triple Extortion
- Before: Attackers would just encrypt your files and demand money to unlock them.
- Now: They not only encrypt your data but also steal it and threaten to leak or sell it on the dark web. Some attackers also hit customers, vendors, or employees with additional extortion.
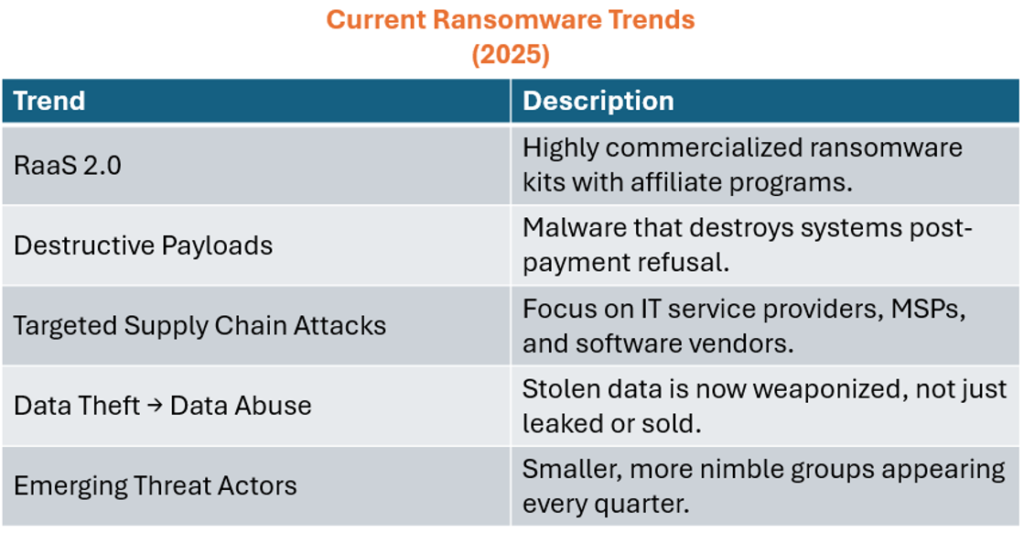
- Ransomware-as-a-Service (RaaS)
- Criminals now offer “ransomware kits” or platforms that anyone can buy and use, making it easier for low-skill attackers to launch major attacks.
- This has lowered the barrier to entry and increased the number of attacks.
- More Targeted Attacks
- Instead of spraying random victims, attackers now go after specific industries (healthcare, energy, government) and large enterprises that can afford big ransoms.
- They spend time doing reconnaissance before deploying the ransomware (like a modern-day heist).
- Supply Chain & Third-Party Attacks
- Rather than attacking one company, attackers are now hitting vendors, service providers, or software companies to gain access to multiple victims downstream.
- The SolarWinds hack was a big wake-up call in this area.
- Destructive Ransomware
- Some new strains don’t just encrypt — they destroy backups, logs, and infrastructure so recovery is harder.
- This forces companies to pay because rebuilding from scratch is devastating.
- Cryptocurrency Obfuscation
- Attackers are getting smarter about how they move ransom payments. They are using crypto mixers, privacy coins (like Monero), or multiple wallet hops to cover their tracks.
- Speed & Automation
- Modern ransomware can spread across entire networks in minutes using automated scripts, stolen admin credentials, and lateral movement tactics.
Scary but True
Ransomware is no longer just “encrypt & extort” — it’s a full-blown business model with sophisticated tactics, better targeting, and way higher stakes. Don’t let your business fall victim! Contact Nieto Technology Partners today to start securing your company’s data. Download our FREE report “How to Create An Effective Cybersecurity Plan” and register to get a FREE high-level assessment of your vulnerabilities.